Exabeam
groupI worked on this project as part of a group. The work shown are assets I collaborated on or produced myself unless otherwise noted.
Responsibilities:
Tools Used:
Overview
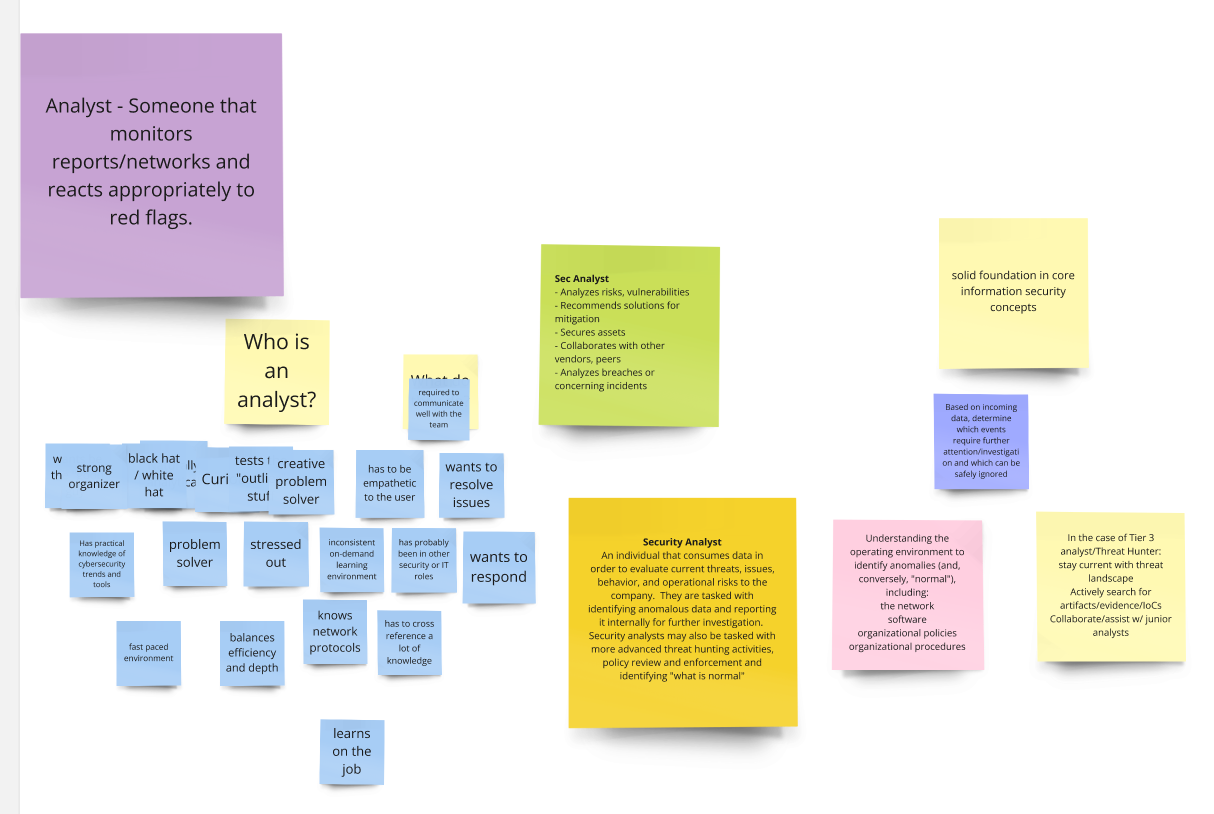
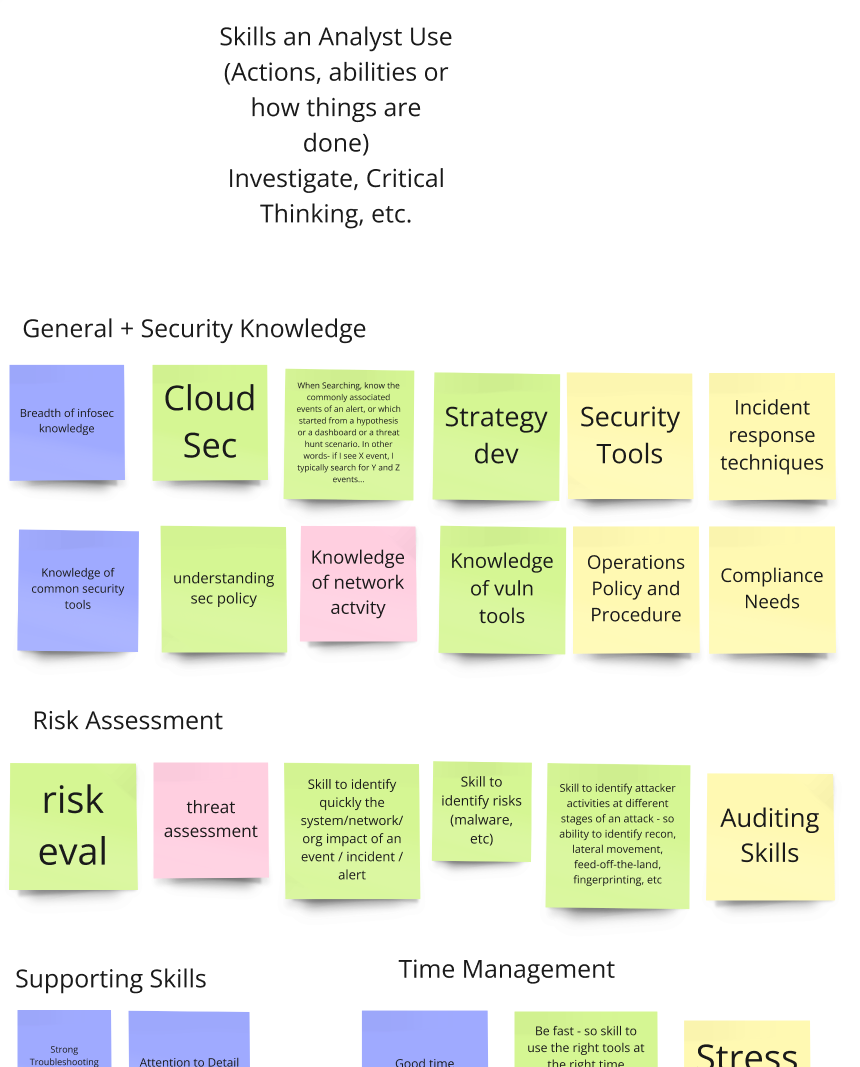
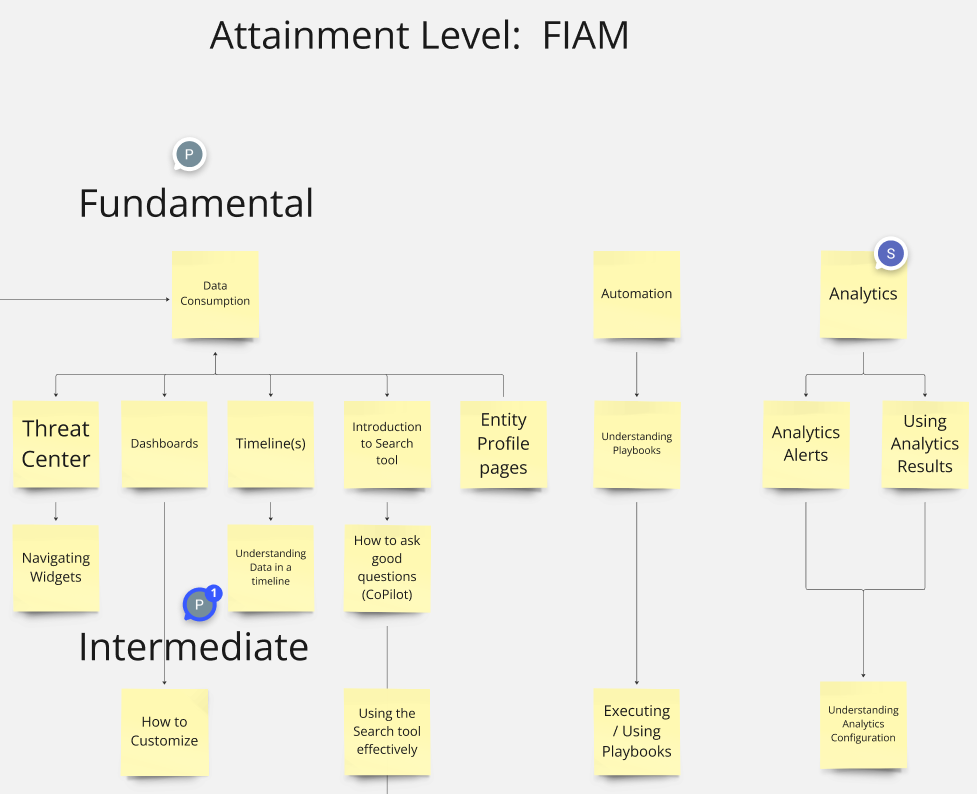
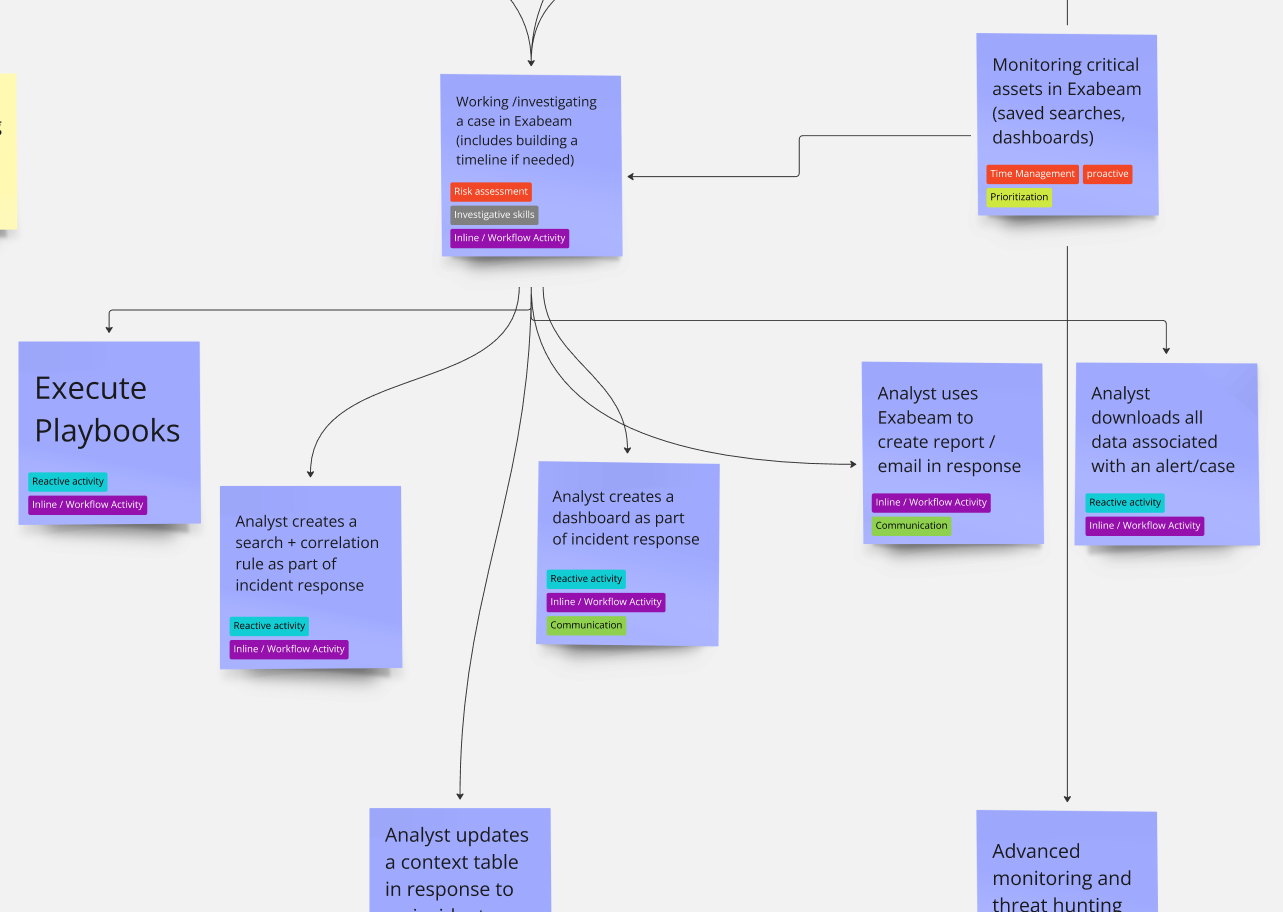
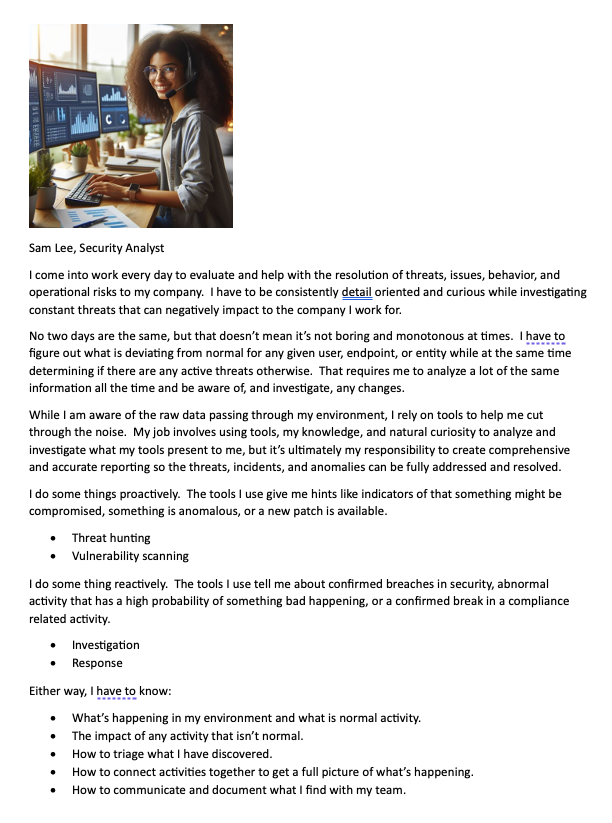
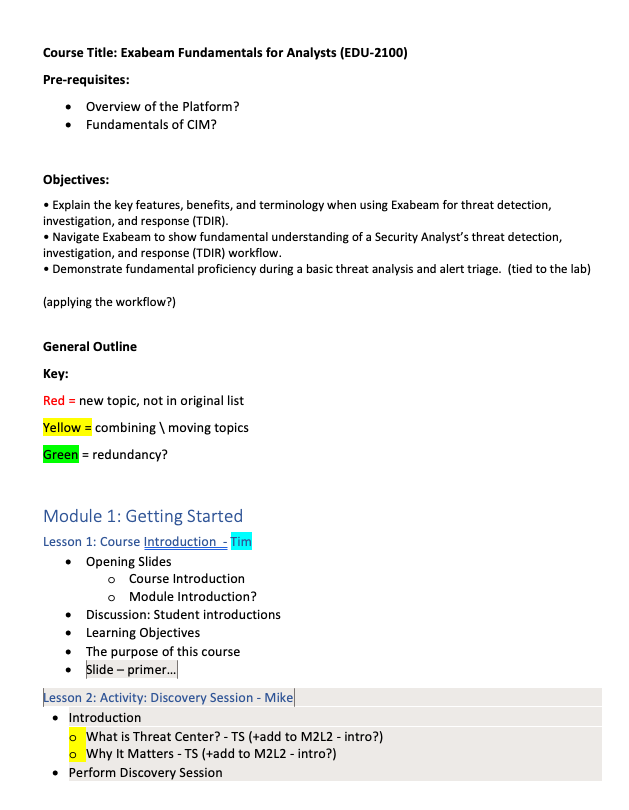
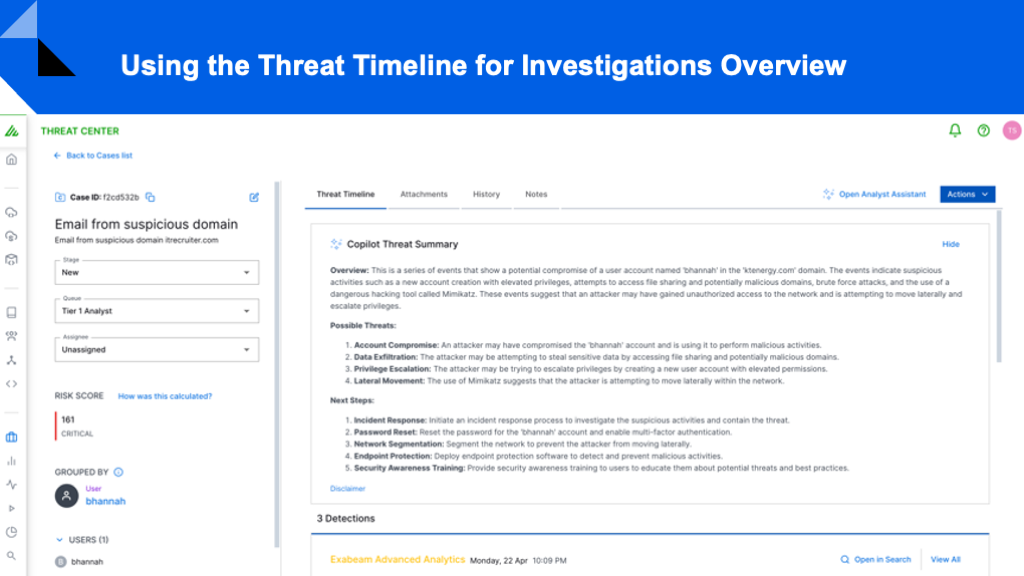
The purpose of this course is to introduce new security analysts to the fundamentals of the Exabeam Security Operations Platform, focusing heavily on the Threat Hunter tool. This tool is a core part of daily operations for security analysts using the tool. It's designed to be comprehensive, meeting analysts at their current career stage and providing hands-on experience with real-world tasks through labs and guided exercises. The course also needs to include instructor-led presentations alongside lab activities for a blended learning experience.
Learning Objectives
- Teach the fundamentals of the platform with a special emphasis on the Threat Hunter tool, which is used daily by analysts.
- Provide hands-on labs for learners to practice tasks in a simulated environment to build confidence in using the platform.
- Target new security analysts while ensuring the course material is comprehensive and digestible, reflecting real-world challenges.